2023년 3월 6일부터 @cloudnet study를 시작 하였다.
[24단계 실습으로 정복하는 쿠버네티스][이정훈 지음]의 책을 기본으로 학습을 한다.
운영을 하면서도 부족한 부분을 배울 수 있을 것이란 기대감과 함께 시작한 수업이나 숙제를 하지 못해서 발생하는 불상사를 경험하지 않고 5주간의 스터디를 잘 마무리 했으면 좋겠다.
3주차 스터디 내용을 정리해 본다.
3주차에는 깃옵스(하버, 깃랩, 아로그시디) 내용을 스터디 하고 실습 진행하였다.
깃옵스 시스템 운영
깃옵스(GitOps)란?
깃옵스는 위브웍스(Weaveworks Inc.)에서 처음 사용한 용어로 프로젝트에 데브옵스를 적용하는 실천 방법 중 하나입니다.
그 중에서도 클라우드 네이티브 애플리케이션을 대상으로 한 지속적 배포(Continuous Deployment)에 초점을 두고 있습니다.
※ 클라우드 네이티브 애플리케이션이 아니어도 깃옵스를 적용할 수 있으나 아래에서 설명드릴 선언형 모델(Declarative Model)을 지원하는 최근 도구들이
클라우드 네이티브에 중점을 두기 때문에 어려움을 겪을 수 있습니다. 위브웍스는 아예 쿠버네티스 대상이라고 못박고 있습니다.
이름에서 나타나듯 애플리케이션의 배포와 운영에 관련된 모든 요소를 코드화하여 깃(Git)에서 관리(Ops)하는 것이 깃옵스의 핵심입니다.
기본 개념은 코드를 이용하여 인프라를 프로비저닝 하고 관리하는 IaC(Infrastructure as Code)에서 나온 것으로 깃옵스는 이를 인프라에서 전체 애플리케이션 범위로 확장하였습니다.
깃옵스(GitOps) 아키텍처
정형화된 깃옵스 아키텍처는 없다.
각 환경에 맞는 솔루션과 서비스를 활용해서 구축하는게 정답이다 생각한다
하지만 기본적인 필요 요소들은 있다
- 소스 형상관리 솔루션
- 소스를 빌드하여서 이미지를 저장하는 레지스트리
- 소스와 이미지를 활용해서 배포 대상 시스템(K8S)에 배포 관리 솔루션
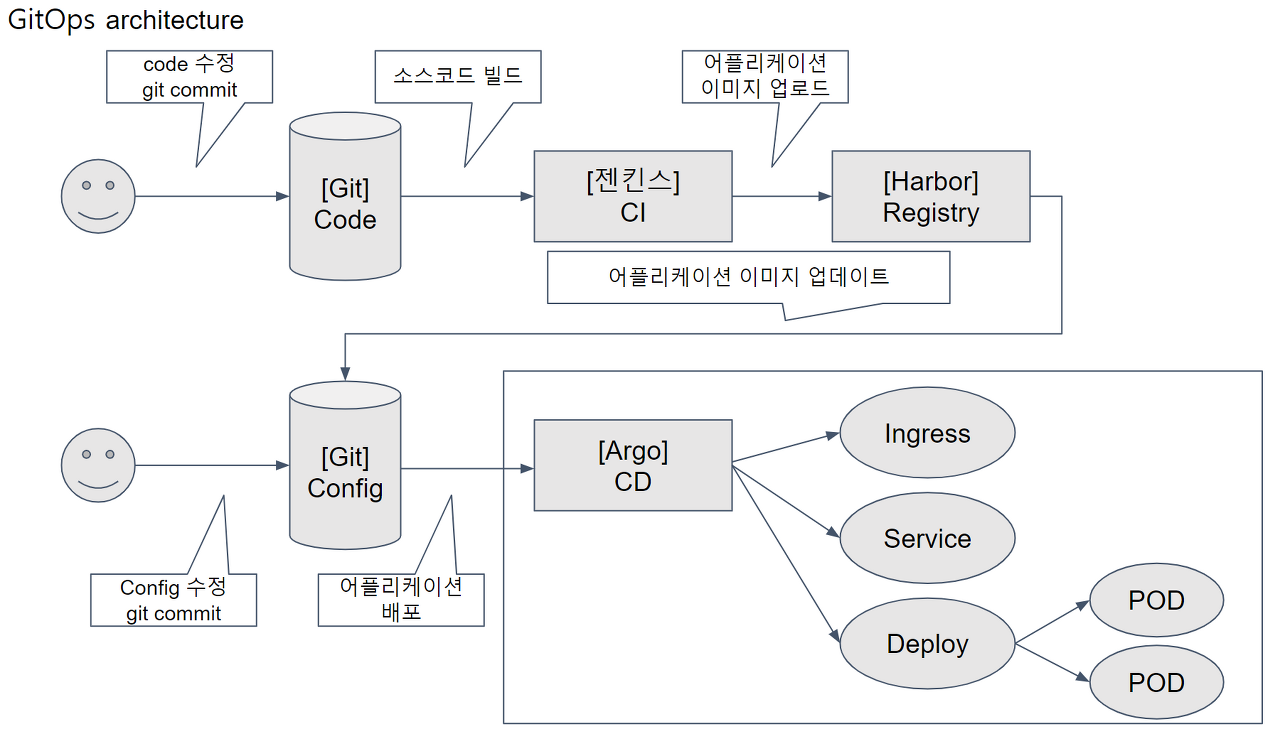
출처 : https://dewble.tistory.com/entry/what-is-gitops
이번 실습에서는
- 소스를 기반으로 이미지로 빌드해서 저장하는
하버(Harbor) - 무료 오픈소스로 사용 가능한 소스코드 원격 저장소
깃랩(GitLab) - 소스와 이미지의 변경사항을 실제 운영환경에 자동 반영해주는
아르고시디(ArgoCD)
에 대해서 학습하고 실제 배포 연동 실습을 진행 하였다.
하버(Harbor) 설치하기
Helm Chart를 활용해서 배포하기
- chart 배포 이전에 Certificate 발급 받아야 한다
- 발급 내용 확인하기
(hj-devstory:default) [root@kops-ec2 ~]# aws acm list-certificates --query 'CertificateSummaryList[].CertificateArn[]' --output text
arn:aws:acm:ap-northeast-2:287481726497:certificate/dda0af88-195e-422e-8c31-c8d5bda7272c
(hj-devstory:default) [root@kops-ec2 ~]# CERT_ARN=`aws acm list-certificates --query 'CertificateSummaryList[].CertificateArn[]' --output text`
(hj-devstory:default) [root@kops-ec2 ~]# echo "alb.ingress.kubernetes.io/certificate-arn: $CERT_ARN"
alb.ingress.kubernetes.io/certificate-arn: 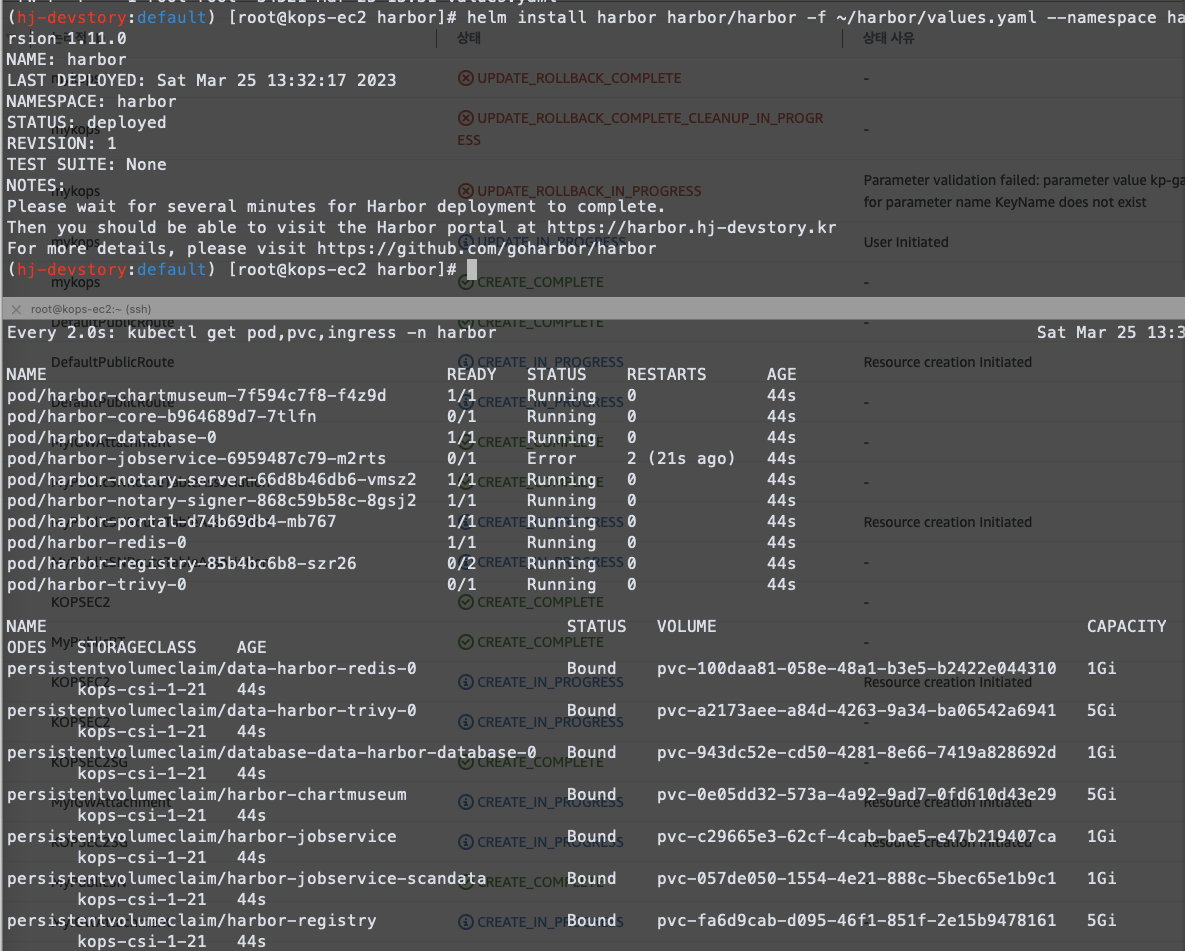
- 하버 헬름 차트 코드를 다운 받아서 values.yaml을 수정한다.
(hj-devstory:default) [root@kops-ec2 ~]# helm repo add harbor https://helm.goharbor.io
"harbor" has been added to your repositories
(hj-devstory:default) [root@kops-ec2 ~]# helm fetch harbor/harbor --untar --version 1.11.0- harbor helm chart 폴더 구성
├── cert
│ ├── tls.crt
│ └── tls.key
├── Chart.yaml
├── conf
│ ├── notary-server.json
│ └── notary-signer.json
├── LICENSE
├── README.md
├── templates
│ ├── chartmuseum
│ │ ├── chartmuseum-cm.yaml
│ │ ├── chartmuseum-dpl.yaml
│ │ ├── chartmuseum-pvc.yaml
│ │ ├── chartmuseum-secret.yaml
│ │ ├── chartmuseum-svc.yaml
│ │ └── chartmuseum-tls.yaml
│ ├── core
│ │ ├── core-cm.yaml
│ │ ├── core-dpl.yaml
│ │ ├── core-pre-upgrade-job.yaml
│ │ ├── core-secret.yaml
│ │ ├── core-svc.yaml
│ │ └── core-tls.yaml
-----
└── values.yaml
17 directories, 68 files- values.yaml 에서 실습 환경에 맞게 수정
vim ~/harbor/values.yaml
----------------------
expose.tls.certSource=none # 19줄
expose.ingress.hosts.core=harbor.<각자자신의도메인> # 36줄
expose.ingress.hosts.notary=notary.<각자자신의도메인> # 37줄
expose.ingress.hosts.core=harbor.gasida.link
expose.ingress.hosts.notary=notary.gasida.link
expose.ingress.controller=alb # 44줄
expose.ingress.className=alb # 47줄~
expose.ingress.annotations=alb.ingress.kubernetes.io/scheme: internet-facing
expose.ingress.annotations=alb.ingress.kubernetes.io/target-type: ip
expose.ingress.annotations=alb.ingress.kubernetes.io/listen-ports: '[{"HTTPS":443}, {"HTTP":80}]'
expose.ingress.annotations=alb.ingress.kubernetes.io/certificate-arn: ${CERT_ARN} # 각자 자신의 값으로 수정입력
alb.ingress.kubernetes.io/scheme: internet-facing
alb.ingress.kubernetes.io/target-type: ip
alb.ingress.kubernetes.io/listen-ports: '[{"HTTPS":443}, {"HTTP":80}]'
alb.ingress.kubernetes.io/certificate-arn: ${CERT_ARN} # 각자 자신의 값으로 수정입력
externalURL=https://harbor.<각자자신의도메인> # 131줄
externalURL=https://harbor.gasida.link- helm chart 배포 수행

- pod, pvc, ingress 들이 정상적으로 배포 된것을 확인 할 수 있다.
Every 2.0s: kubectl get pod,pvc,ingress -n harbor Sat Mar 25 13:35:12 2023
NAME READY STATUS RESTARTS AGE
pod/harbor-chartmuseum-7f594c7f8-f4z9d 1/1 Running 0 2m52s
pod/harbor-core-b964689d7-7tlfn 1/1 Running 0 2m52s
pod/harbor-database-0 1/1 Running 0 2m52s
pod/harbor-jobservice-6959487c79-m2rts 1/1 Running 3 (2m12s ago) 2m52s
pod/harbor-notary-server-66d8b46db6-vmsz2 1/1 Running 0 2m52s
pod/harbor-notary-signer-868c59b58c-8gsj2 1/1 Running 0 2m52s
pod/harbor-portal-d74b69db4-mb767 1/1 Running 0 2m52s
pod/harbor-redis-0 1/1 Running 0 2m52s
pod/harbor-registry-85b4bc6b8-szr26 2/2 Running 0 2m52s
pod/harbor-trivy-0 1/1 Running 0 2m52s
NAME STATUS VOLUME CAPACITY ACCESS M
ODES STORAGECLASS AGE
persistentvolumeclaim/data-harbor-redis-0 Bound pvc-100daa81-058e-48a1-b3e5-b2422e044310 1Gi RWO
kops-csi-1-21 2m52s
persistentvolumeclaim/data-harbor-trivy-0 Bound pvc-a2173aee-a84d-4263-9a34-ba06542a6941 5Gi RWO
kops-csi-1-21 2m52s
persistentvolumeclaim/database-data-harbor-database-0 Bound pvc-943dc52e-cd50-4281-8e66-7419a828692d 1Gi RWO
kops-csi-1-21 2m52s
persistentvolumeclaim/harbor-chartmuseum Bound pvc-0e05dd32-573a-4a92-9ad7-0fd610d43e29 5Gi RWO
kops-csi-1-21 2m52s
persistentvolumeclaim/harbor-jobservice Bound pvc-c29665e3-62cf-4cab-bae5-e47b219407ca 1Gi RWO
kops-csi-1-21 2m52s
persistentvolumeclaim/harbor-jobservice-scandata Bound pvc-057de050-1554-4e21-888c-5bec65e1b9c1 1Gi RWO
kops-csi-1-21 2m52s
persistentvolumeclaim/harbor-registry Bound pvc-fa6d9cab-d095-46f1-851f-2e15b9478161 5Gi RWO
kops-csi-1-21 2m52s
NAME CLASS HOSTS ADDRESS PORTS AGE
ingress.networking.k8s.io/harbor-ingress alb harbor.hj-devstory.kr 80, 443 2m52s
ingress.networking.k8s.io/harbor-ingress-notary alb notary.hj-devstory.kr 80, 443 2m52s- 배포 웹 주소 확이 및 접근
(hj-devstory:default) [root@kops-ec2 harbor]# echo -e "harbor URL = https://harbor.$KOPS_CLUSTER_NAME"
harbor URL = https://harbor.hj-devstory.kr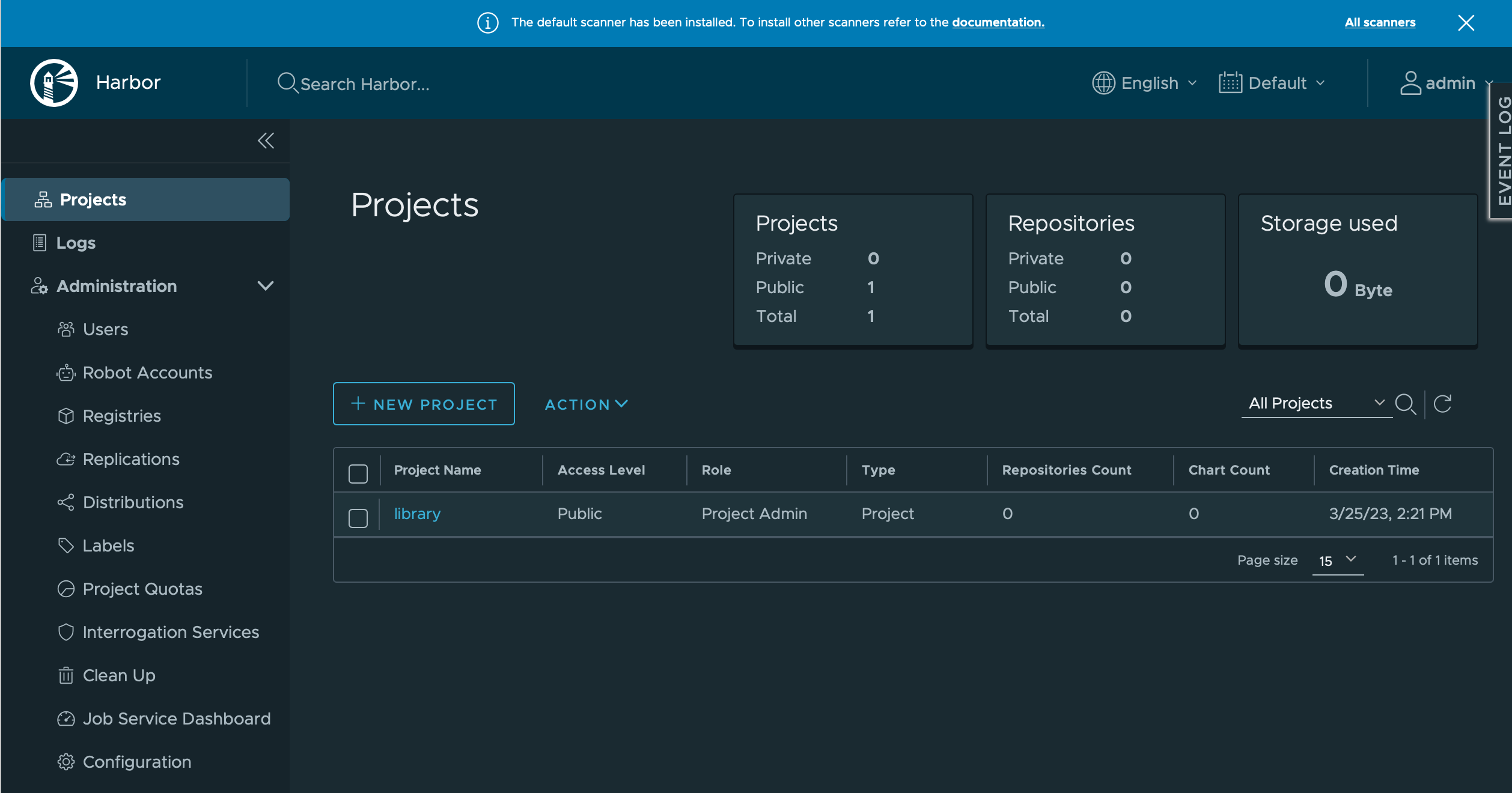
- 프로젝트 생성

깃랩(GitLab) 구축하기
- 깃랩 헬름차트 사용
(hj-devstory:default) [root@kops-ec2 harbor]# helm repo add gitlab https://charts.gitlab.io/
"gitlab" has been added to your repositories
(hj-devstory:default) [root@kops-ec2 harbor]# helm repo update
Hang tight while we grab the latest from your chart repositories...
...Successfully got an update from the "harbor" chart repository
...Successfully got an update from the "gitlab" chart repository
Update Complete. ⎈Happy Helming!⎈
(hj-devstory:default) [root@kops-ec2 harbor]# helm fetch gitlab/gitlab --untar --version 6.8.1- 깃랩 차트 폴더 확인
(hj-devstory:default) [root@kops-ec2 gitlab]# tree
.
├── CHANGELOG.md
├── charts
│ ├── cert-manager
│ │ ├── Chart.yaml
│ │ ├── README.md
│ │ ├── templates
│ │ │ ├── cainjector-deployment.yaml
│ │ │ ├── cainjector-psp-clusterrolebinding.yaml
│ │ │ ├── cainjector-psp-clusterrole.yaml
│ │ │ ├── cainjector-psp.yaml
│ │ │ ├── cainjector-rbac.yaml
│ │ │ ├── cainjector-serviceaccount.yaml
------
│ │ ├── configmap.yaml
│ │ ├── _generate_secrets.sh.tpl
│ │ ├── job.yaml
│ │ ├── rbac-config.yaml
│ │ └── self-signed-cert-job.yml
│ ├── _shell.tpl
│ ├── _suggested_reviewers.tpl
│ ├── upgrade_check_hook.yaml
│ └── _workhorse.tpl
└── values.yaml
74 directories, 561 files- values.yaml을 실습 환경에 맞게 수정
vim ~/gitlab/values.yaml
----------------------
global:
hosts:
domain: <각자자신의도메인> # 52줄
https: true
ingress: # 66줄~
configureCertmanager: false
provider: aws
class: alb
annotations:
alb.ingress.kubernetes.io/scheme: internet-facing
alb.ingress.kubernetes.io/target-type: ip
alb.ingress.kubernetes.io/listen-ports: '[{"HTTPS":443}, {"HTTP":80}]'
alb.ingress.kubernetes.io/certificate-arn: ${CERT_ARN} # 각자 자신의 값으로 수정입력
alb.ingress.kubernetes.io/success-codes: 200-399
alb.ingress.kubernetes.io/group.name: "gitlab"
tls: # 79줄
enabled: false
----------------------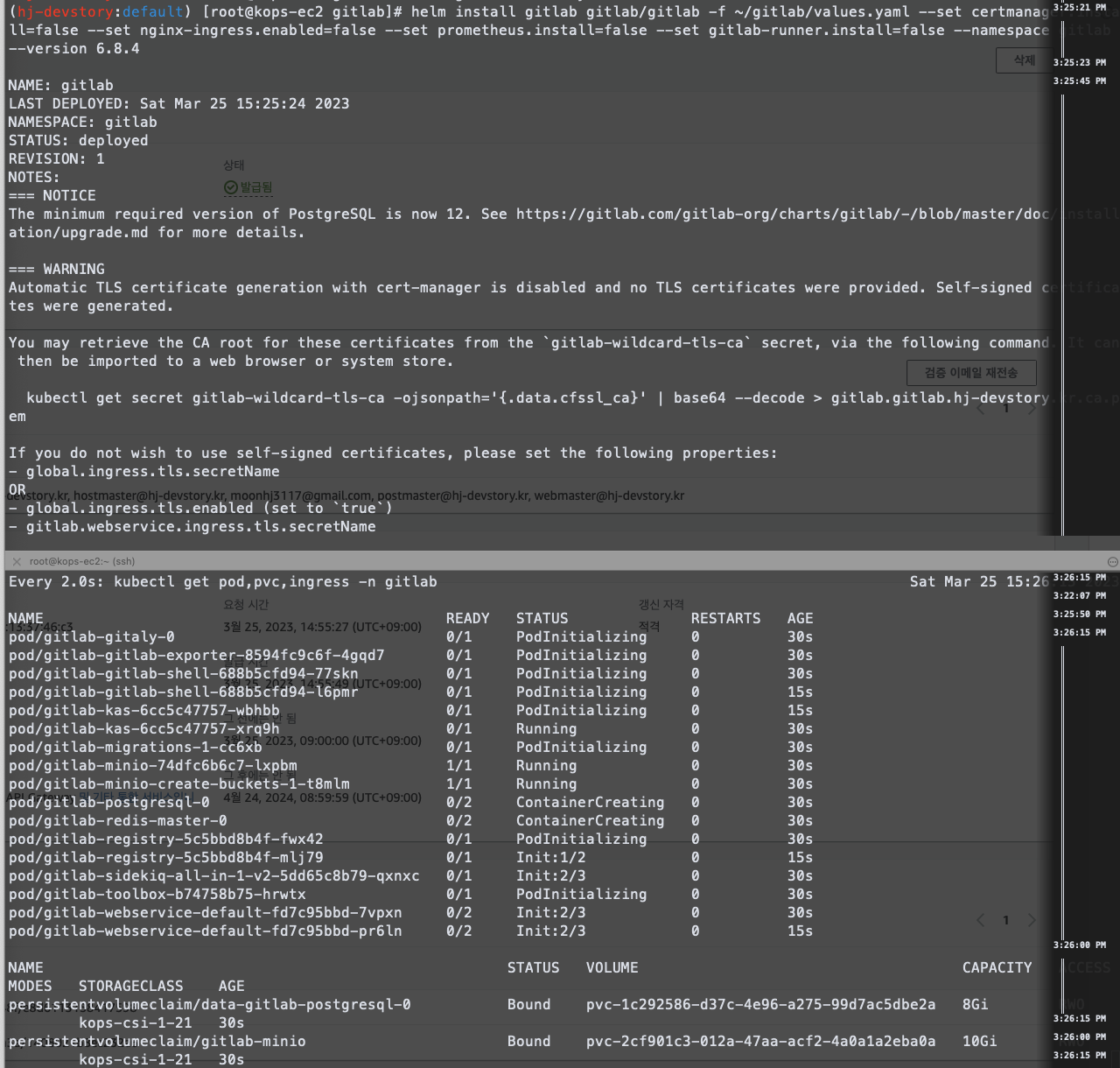
- gitlab ingress 확인
(hj-devstory:default) [root@kops-ec2 gitlab]# kubectl get ingress -n gitlab
NAME CLASS HOSTS ADDRESS PORTS AGE
gitlab-kas alb kas.gitlab.hj-devstory.kr k8s-gitlab-442b80e6b2-1422079830.ap-northeast-2.elb.amazonaws.com 80 2m3s
gitlab-minio alb minio.gitlab.hj-devstory.kr k8s-gitlab-442b80e6b2-1422079830.ap-northeast-2.elb.amazonaws.com 80 2m3s
gitlab-registry alb registry.gitlab.hj-devstory.kr k8s-gitlab-442b80e6b2-1422079830.ap-northeast-2.elb.amazonaws.com 80 2m3s
gitlab-webservice-default alb gitlab.gitlab.hj-devstory.kr k8s-gitlab-442b80e6b2-1422079830.ap-northeast-2.elb.amazonaws.com 80 2m3s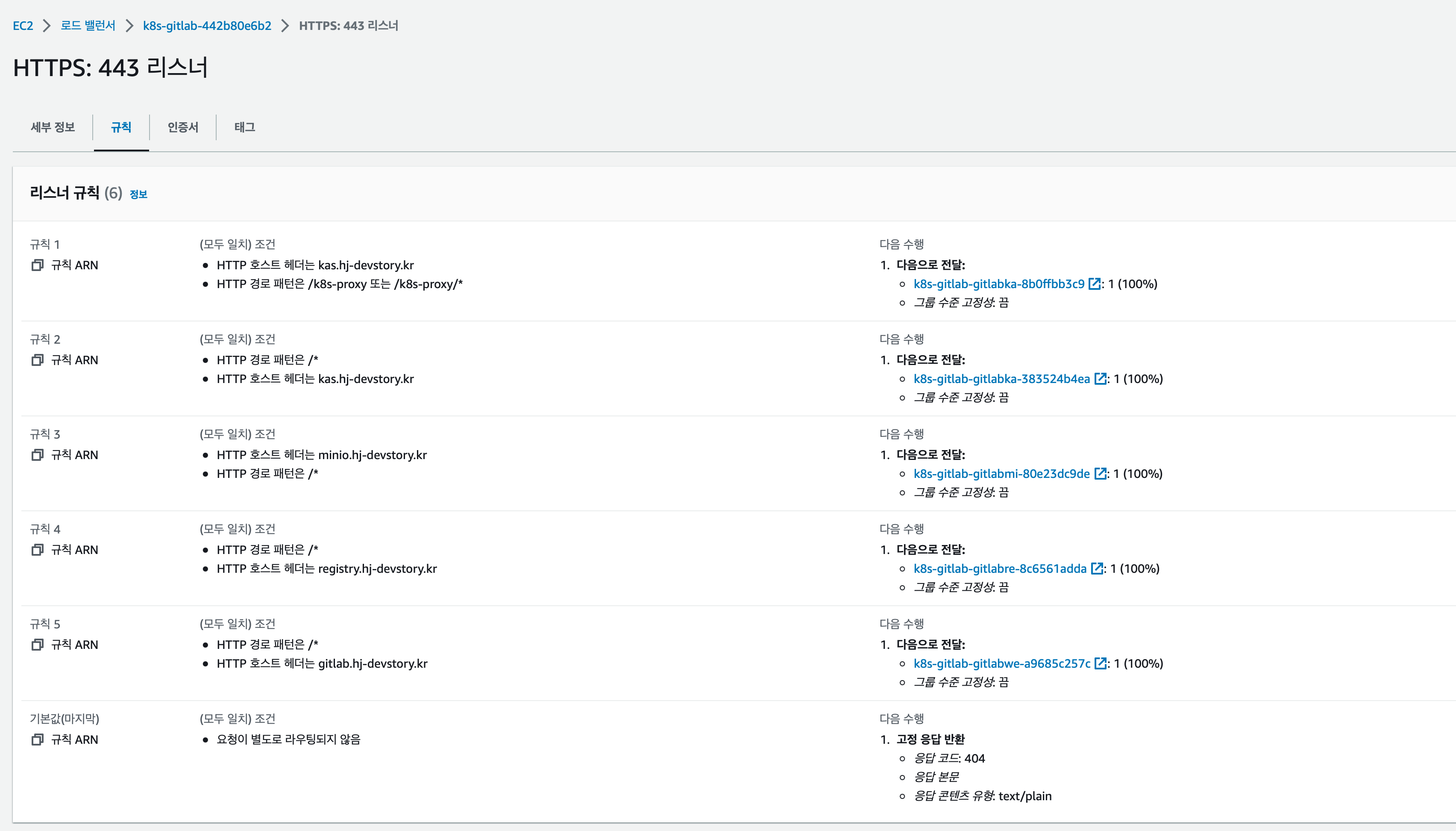

아르고시디(ArgoCD) 설치하기
- 아르고시디는 GitOps에서 쿠버네티스 배포를 담당하는 툴 이다.
- 지속적인 배포를 위해서 Applications에 등록 된 Git을 주기적으로 트래킹 하면서 변경사항을 Kubernetes에 배포하는 역할을 담당한다
- 이번에는 ArgoCD Helm Charts에서 별다른 values변경 없이 바로 배포한다
helm repo add argo https://argoproj.github.io/argo-helm
helm repo update
(hj-devstory:gitlab) [root@kops-ec2 ~]# helm install argocd argo/argo-cd --set server.service.type=LoadBalancer --namespace argocd --version 5.19.14
NAME: argocd
LAST DEPLOYED: Sun Mar 26 00:26:57 2023
NAMESPACE: argocd
STATUS: deployed
REVISION: 1
TEST SUITE: None
NOTES:
DEPRECATED option createAggregateRoles - Use global.rbac.aggregatedRoles
In order to access the server UI you have the following options:
1. kubectl port-forward service/argocd-server -n argocd 8080:443
and then open the browser on http://localhost:8080 and accept the certificate
2. enable ingress in the values file `server.ingress.enabled` and either
- Add the annotation for ssl passthrough: https://argo-cd.readthedocs.io/en/stable/operator-manual/ingress/#option-1-ssl-passthrough
- Set the `configs.params."server.insecure"` in the values file and terminate SSL at your ingress: https://argo-cd.readthedocs.io/en/stable/operator-manual/ingress/#option-2-multiple-ingress-objects-and-hosts
After reaching the UI the first time you can login with username: admin and the random password generated during the installation. You can find the password by running:
kubectl -n argocd get secret argocd-initial-admin-secret -o jsonpath="{.data.password}" | base64 -d
(You should delete the initial secret afterwards as suggested by the Getting Started Guide: https://argo-cd.readthedocs.io/en/stable/getting_started/#4-login-using-the-cli)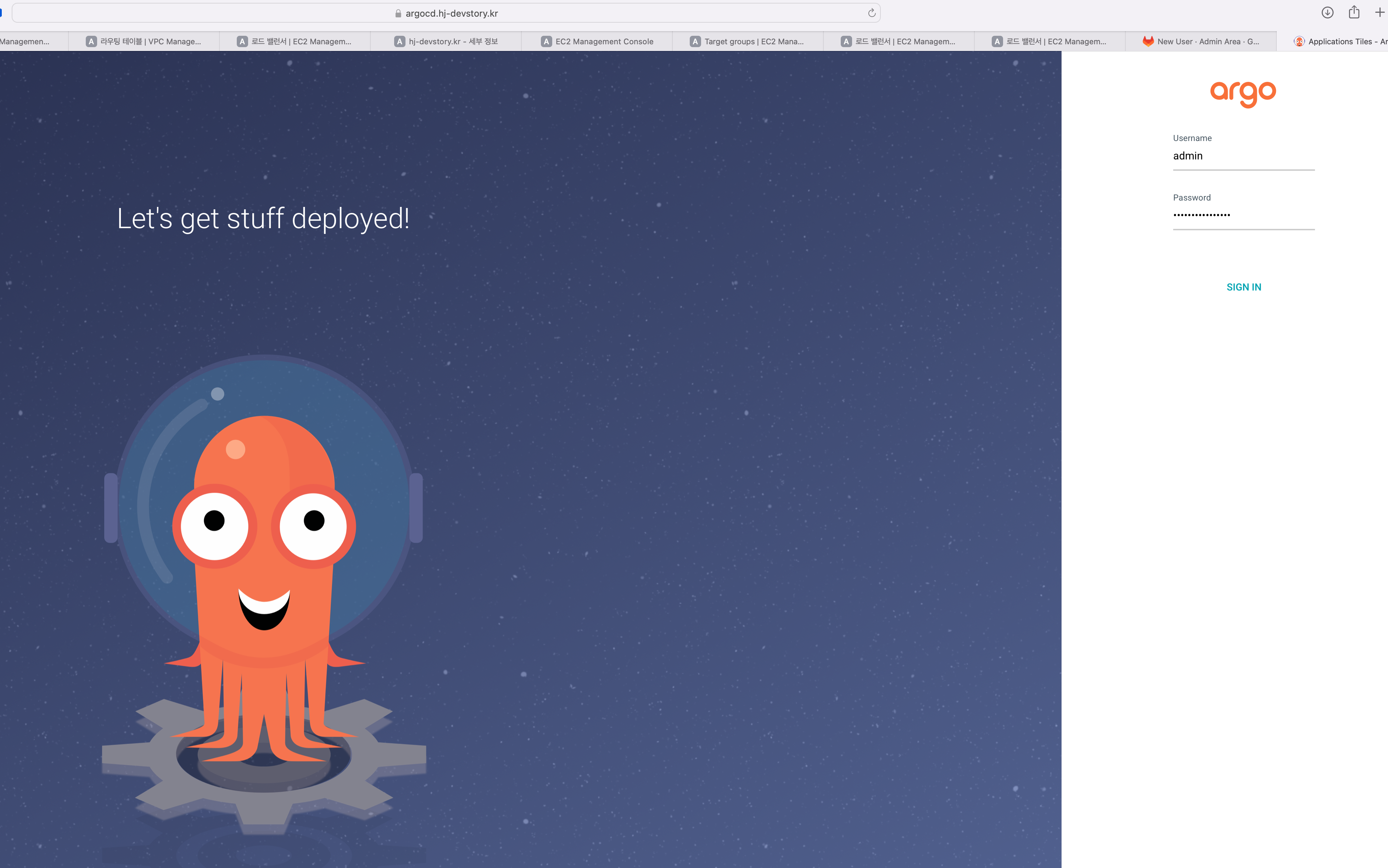
- ArgoCD 접속을 위한 서비스 구성은 끝났다.
- ArogCD에서 배포의 대상 클러스터를 추가하는 작업을 수행한다.
- 터미널에서 Argocd 커맨드를 다운 받아서 클러스터 추가 작업을 수행한다
(hj-devstory:gitlab) [root@kops-ec2 ~]# curl -sSL -o argocd-linux-amd64 https://github.com/argoproj/argo-cd/releases/latest/download/argocd-linux-amd64
(hj-devstory:gitlab) [root@kops-ec2 ~]# install -m 555 argocd-linux-amd64 /usr/local/bin/argocd
(hj-devstory:gitlab) [root@kops-ec2 ~]# chmod +x /usr/local/bin/argocd
#### argocd version check
(hj-devstory:gitlab) [root@kops-ec2 ~]# argocd version --short
argocd: v2.6.7+5bcd846
#### argocd cluster 추가
(hj-devstory:gitlab) [root@kops-ec2 ~]# argocd login argocd.$KOPS_CLUSTER_NAME --username admin --password $ARGOPW
WARNING: server certificate had error: x509: certificate is valid for localhost, argocd-server, argocd-server.argocd, argocd-server.argocd.svc, argocd-server.argocd.svc.cluster.local, not argocd.hj-devstory.kr. Proceed insecurely (y/n)? y
'admin:login' logged in successfully
Context 'argocd.hj-devstory.kr' updated
#### 추가 된 argocd 클러스터 리스트 조회
(hj-devstory:gitlab) [root@kops-ec2 ~]# argocd cluster list
SERVER NAME VERSION STATUS MESSAGE PROJECT
https://kubernetes.default.svc in-cluster Unknown Cluster has no applications and is not being monitored.결론
- git을 통한 소스 관리 및 빌드 실행을 담당하는 gitlab
- 빌드 된 이미지의 저장소로 사용하는 harbor
- 빌드 된 이미지와 코드들을 트래킹하면서 쿠버네티스에 배포를 담당하는 argocd
- 각 솔루션들의 기본적인 특징과 설치 방법에 대해서 정리해 보았다
- 실제로 각 서비스들을 활용해서 이미지가 빌드 되고 자동 배포되는 환경은 다음 포스팅에서 정리하 도록 하겠다.